Hot Hardware: Avoid This Virus Laden Version Of WhatsApp And Delete It From Your Phone
2021-08-31 11:36

Avoid This Virus Laden Version Of WhatsApp And Delete It From Your Phone Now
by Nathan Ord -Hot Hardware
It is somewhat common for enterprising developers to add features to popular apps via plug-ins, companion apps, or even by modifying the original when possible. By reverse-engineering apps, like WhatsApp for example, a skilled developer can tweak and modify features or even add their own spin on things. However, this also opens the door to malicious possibilities, as we have now seen with an infected version of FMWhatsApp, which is a popular WhatsApp mod.
FMWhatsApp typically adds themes, read receipt controls, more robust file attachment capabilities, and more. While all of that may sound well and good, researchers at Kaspersky recently found that the trojan Triada has also managed to sneak into FMWhatsApp in version 16.80.0, by exploiting a hole in the advertising software development kit.
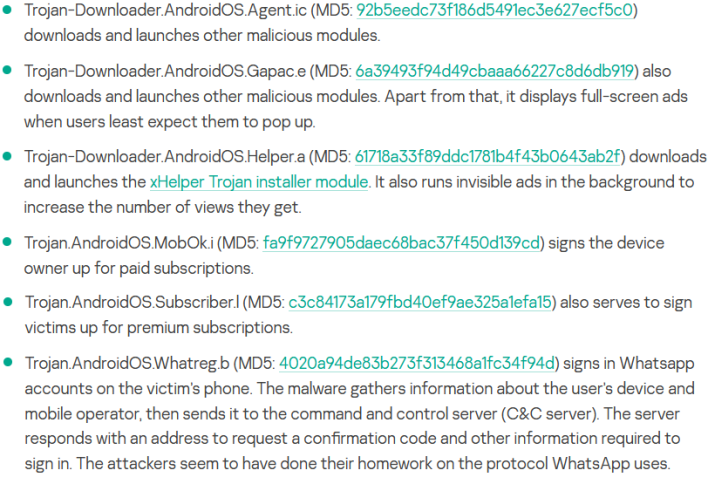
Triada works after the app is launched, when the malware gathers unique device identifiers, including the name of the Android app package that it is contained in. This information is then sent off to a remote server that registers the device and returns a link to a malicious payload that is then downloaded, decrypted, and installed by the trojan. With this, Kaspersky has identified six different types of malware being downloaded by Triada, which all go off and do separate things.
The most obvious step to protect yourself against such malware is to not download apps from unofficial sources. Although not foolproof, it is best to download approved apps from an app store and request features from the developer, which may eventually be implemented, especially if they are already available by popular mods.
Other than that, always keep your phone patched and up to day, keep an eye on what permissions you grant apps and perhaps install a mobile antivirus utility to add an extra layer of protection. At the end of the day, though, it seems that the general rule of “do not randomly download things off the internet” prevails, and this incident further drives that point home.









